This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
Friday 18th September 2020
BLOG: Poor attack surface management means the threat from targeted ransomware persists
By Jamie MacColl
In this blog post, we explain how and why many organisations are still vulnerable to the threats posed by targeted ransomware operations.
The emergence of targeted ransomware operations has been one of the defining features of the cyber threat landscape in recent years. To date, ransomware groups has used a variety of approaches, but increasingly prize so- called ‘big-game’ tactics, which them to extract sizeable ransoms large organisations. Although this threat is by now well-established, Orpheus’ Cyber Risk Rating tool illustrates that many organisations – both big and small – remain vulnerable to the tactics and techniques used by ransomware operations, particularly those that target remote access vulnerabilities and services.
The emergence of targeted ransomware operations
Historically, the majority of ransomware variants were distributed via mass spam campaigns (see Figure 1) that demanded small ransoms and were indiscriminate in targeting home users or businesses. In 2018, however, a number of ransomware operators shifted their approach to specifically target businesses or governments in order to extract higher ransom payments. Typically, they infect their victims via poorly secured remote access services such as RDP instances, either by scanning for them (see Figure 1) or purchasing access via dedicated cybercriminal marketplaces or by contracting cybercriminal groups to compromise them.
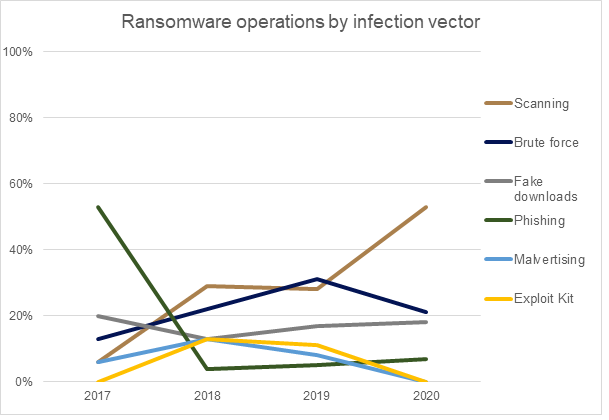
Figure 1: Orpheus’ intelligence reporting database illustrates the growth of ransomware operations that scan for open ports or vulnerabilities.
Until this year, exposed RDP or other Remote Desktop Service compromised via default credentials or brute-force attacks remained the most popular infection vector for targeted ransomware operations (see Figure 2). While this vector remains popular, ransomware operators now also seek to infect victims by scanning for and exploiting vulnerabilities in remote access tools and services such as VPNs (see Figure 3). Most notably:
- CVE-2019-19781, which affects Citrix Application Delivery Controller and Citrix Gateway, and has been exploited by the Maze, Sodinokibi, Ragnorak and DoppelPaymer ransomware gangs against victims in a variety of sectors.
- CVE-2019-11510, which affects Pulse Secure VPN Gateway, which the Sodinokibi ransomware group exploited to compromise Travelex.
- CVE-2019-0708, a wormable vulnerability affecting Windows 7 and 2008 servers.
- CVE-2020-5902, which affects F5 BIG-IP Application Delivery Controllers and has been exploited by both nation-state and cybercriminal groups.
As we have noted in a previous blog post, these vulnerabilities are will remain attractive because of the high-level of access they provide and the lifetime of these vulnerabilities. The latter is due to the slow response from many organisations in identifying and patching them. This is partly due to the general difficulties inherent in vulnerability management, but also due to factors related to the COVID-19 pandemic, which has significantly increased the workload of IT staff and the attack surfaces they are trying to manage.
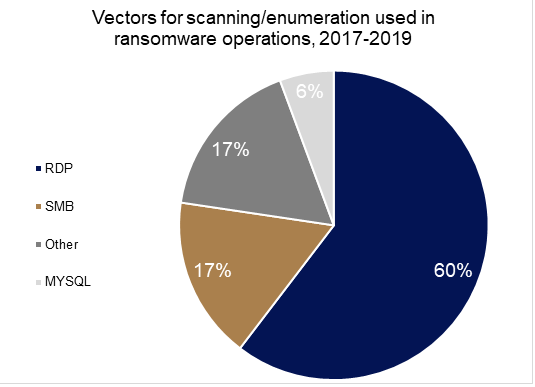
Figure 2: from 2017-19, the majority of targeted ransomware operations infected victims via poorly secured RDP instances.
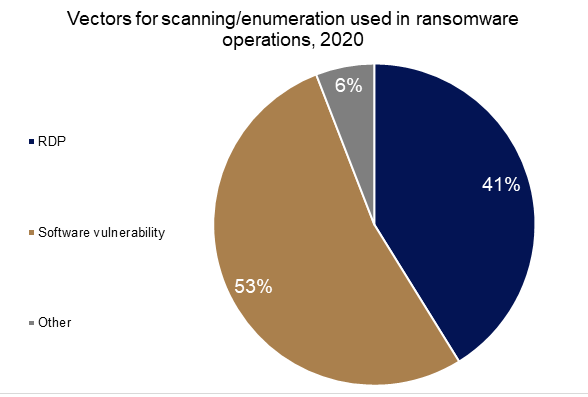
Figure 3: Orpheus’ intelligence reporting database highlights that in 2020, ransomware operators shifted to scanning for and exploiting known software vulnerabilties.
Orpheus’ Cyber Risk Rating highlights poor attack surface management
However, despite the threat posed by ransomware operations targeting poorly secured remote access services or exploiting vulnerabilities, many organisations appear unaware of how their attack surface might present an attractive target. Using Orpheus Cyber Risk Rating tool, we passively scanned the attack surface of more than 45,000 organisations, and found that a number of them remain vulnerable to tactics employed by targeted ransomware operators. For instance, as Figure 4 illustrates, 2544 organisations have open ports associated with remote desktop services, with the majority involving port 3389 (RDP). Although RDP instances can be exposed and not necessarily vulnerable if hardened with proper authentication processes, it is still poor cyber hygiene to leave them internet-facing
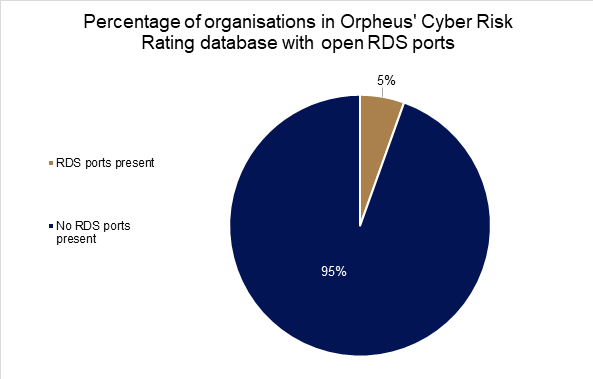
Figure 4: Orpheus’ Cyber Risk Rating tool illustrates how organisations continue to use open RDS ports.
While we detected a much small number of organisations with remote access vulnerabilities on their internet-facing infrastructure (see Figure 5), it is still notable that we are detecting these vulnerabilities several months or even a year after they have been patched. Moreover, several organisations where we detected vulnerabilities – particularly those with CVE-2019-19781 or CVE-2020-5902 – are either large corporations or governmental organisations that would be attractive targets for big-game hunters.
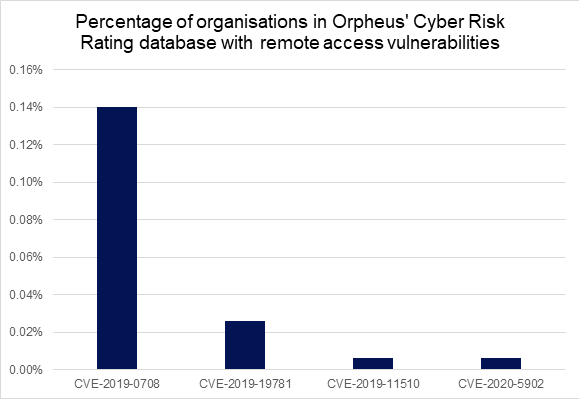
Figure 5: Orpheus’ Cyber Risk Rating tool shows that 80 companies in our database have remote access vulnerabilities on their internet-facing infrastructure.
Managing risk and mitigating threats
Mitigating the threat from targeted ransomware operations requires a threat-led and risk-based approach. Combining these two approaches and taking an attacker’s perspective to understand your attack surface allows you to reduce the level of cyber risk that you face.
If you would like to see your Cyber Risk Rating, or to understand what threats could affect you from your third party suppliers, contact us for a demonstration of our Cyber Risk Management platform.
Get our latest cyber intelligence insights straight into your inbox
Fill out the short form below to subscribe to our newsletter so that you never miss out on our cyber intelligence insights and news.
