This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
Thursday 16th January 2020
The Implications of Rising US-Iran Tensions for Businesses
The targeted assassination of Iranian general Qasem Soleimani on 3 January 2020, on the orders of President Trump, ratcheted up US-Iranian tensions, leading to forecasts of impending Third World War. Although the official Iranian response in the form of a missile strike on an Iraqi military base appeared to be a calculated attempt to de-escalate the situation and reduce the prospect of further military conflict, we anticipate the renewed hostilities will also have significant implications on the cyber threat landscape for Western businesses. In this blog piece we explain why western companies face a heightened threat level from Iranian groups in the wake of increasing US-Iranian tensions, and why it is vital for firms to familiarise themselves with Iranian TTPs (tactics, techniques and procedures).
We anticipate that in line with past behaviour, Iranian threat groups will respond to the targeted assassination of Quasem Soleimani with increased cyber attacks on Western businesses – possibly under the auspices of an Iranian activist group. We believe this will most likely target financial institutions, elements of critical national infrastructure (CNI) or government organisations. This reinforces the need to understand Iranian state actors, their TTPs, and likely targets.
Iran’s history of retaliation
It is a fact of 21st century diplomacy that deteriorating geopolitical relations can lead to an malicious cyber activity, as Iran has previously demonstrated. The regime is no stranger to using offensive cyber capabilities when seeking to stop short of conventional military efforts. Indeed, the degree of deniability associated with cyber attacks and the ability to use or attribute operations to third-parties corresponds perfectly with Iran’s established state sponsorship of designated terrorist entities, such as Hezbollah in Lebanon and the Popular Mobilization Forces in Iraq.
For example, in February 2014 an Iranian threat group targeted Sands Hotel and Casino’s systems with data wiping malware, ultimately costing the casino at least USD 40 million.[1] The operation – claimed by a fabricated activist group called the Anti WMD team – was launched in response to the casino’s owner and prominent Republican donor, Sheldon Adelson, publicly advocated detonating an American warhead on Iranian soil. While Adelson was a private citizen, it reflects a willingness to reply to perceived threats and insults with destructive cyber operations.
Cyber retaliation attacks are not limited to private individuals, however. In response to sanctions placed on Iran under the Obama administration, Iranian groups in 2012 used DDoS attacks against numerous financial institutions, including Bank of America Corp., and Wells Fargo, with Distributed Denial of Service (DDoS) attacks. Once again, the attack was claimed by a third party, going by the name the Izz al-Din al-Qassam Cyber Fighters. However, this claim was disputed by industry experts who attributed to attack to the Iranian state.[2] The attacks were relatively inconsequential for the banks’ customers but cost the companies millions of dollars to maintain their websites over the period of the attacks. A 2016 US Department of Justice indictment accused seven Iranians working for the Iranian government of launching DDoS attacks against 46 different businesses, mostly financial institutions.[3]
Historical
precedent of Iran resorting to asymmetric cyber responses in retaliation to
either perceived insults or increasing geopolitical tensions underlines the
need for western businesses to familiarise themselves with Iranian TTPs.

Iranian state groups
Since the 2009 deployment of Stuxnet, a highly sophisticated US-Israeli worm which caused substantial damage to Iran’s nuclear programme, Iran has accelerated its efforts to develop significant offensive capabilities of its own. While much of its activity is directed at perceived domestic threats to the regime such as human rights activists or dissidents, it frequently launches successful attacks on foreign businesses and governments.
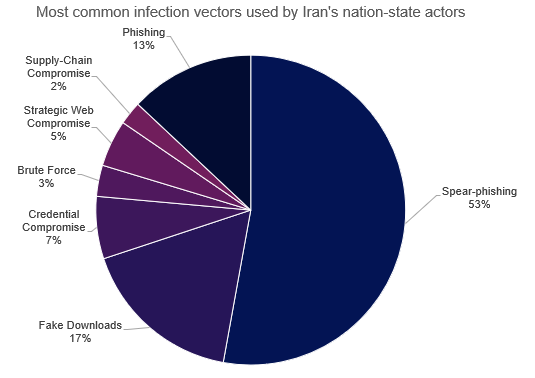
In terms of TTPs, Iranian state actors prefer spear-phishing as an initial infection vector, often accompanied by extensive social engineering campaigns, as illustrated in the below image. This is typically followed by infrastructure enumeration on victims’ computers before deploying malware. Iranian state espionage groups frequently access their target environment by using password spraying, web shells, and a mixture of custom and commodity tooling.[4][5]
In terms of targeting, as Iran will likely seek to conduct operations with tangible effects, we assess they will likely target critical national infrastructure in the financial and energy sectors, or possibly entities in the government or defence sectors. Attacks would likely target Industrial Control Systems, or other business critical systems to cause disruption. Alternatively, they could attempt to wipe valuable data, a tactic frequently used by Iran, as illustrated by both its older wiper malware Shamoon, and the newer Dustman variant. This would fit the criteria of an asymmetric response, without necessitating US retaliation.
These organisations do not need to be located within the US to be an attractive target for Iranian capabilities. UK branches of American multi-national corporations also face an increased threat. For example, disrupting the operations of the London offices of a US bank would provide a symbolic victory for the Iranian regime. Moreover, as President Trump has significant, highly visible business interests overseas, there is also the possibility his assets in the hospitality sector will be targeted.
Threat groups attempting to run these operations could leverage intelligence gathered by the frequent espionage operations conducted by Iranian threat groups targeting US organisations.
Conclusion
We recommend Western organisations familiarise themselves with the increasing threat posed by Iranian nation state groups. This is especially important for firms operating in sectors that we assess face a higher threat. The threat intelligence regarding relevant APT groups and their TTPs could help prevent significant disruption to operations, protecting businesses during periods of pronounced geo-political upheaval.
[1]https://www.vox.com/recode/2020/1/7/21055715/iran-cyber-attack-threat-soleimani
[2] https://www.csoonline.com/article/2132319/bank-attackers-more-sophisticated-than-typical-hacktivists–expert-says.html
[3] https://www.justice.gov/opa/pr/seven-iranians-working-islamic-revolutionary-guard-corps-affiliated-entities-charged
[4] https://www.cyberscoop.com/nsa-iran-cyber-operations-david-hogue/
[5] https://www.zdnet.com/article/source-code-of-iranian-cyber-espionage-tools-leaked-on-telegram/
Get our latest cyber intelligence insights straight into your inbox
Fill out the short form below to subscribe to our newsletter so that you never miss out on our cyber intelligence insights and news.
