By Orpheus Analysts
In the fifth part of our series on the long-term implications of COVID-19 for the cyber threat landscape, we assess the future of domestic and international legislation and regulation. You can read the introduction to the series here.
Introduction
COVID-19 has led to the rapid expansion of flexible working arrangements. In sectors such as healthcare, which have traditionally been resistant to digitalisation, this has led to a new variety of new entities collecting and processing data. The speed of this transformation, however, has raised questions about the suitability and capabilities of existing legislation and regulation. The balancing act between data collection for public health, and privacy and security concerns, has become more delicate as governments turn to contract-tracing apps and other forms of bio-surveillance to manage the pandemic.
This shift towards digitalisation, and the increasing importance of the healthcare and pharmaceutical sectors, has also introduced new opportunities for threat actors looking to exploit the pandemic. Their willingness to target these sectors has also raised questions about the lack of an international legal framework to protect organisations essential to the COVID-19 response.
This blog assesses that existing domestic legal and regulatory frameworks are insufficient to keep up with technological shifts. In the short term, the impact of COVID-19 on domestic cyber security regulation, legislation and enforcement is likely to have little if any impact on either the capability or intent of threat actors, or on the ability of organisations to defend themselves against cyber threats. In the longer term, however, it is assessed that it will exacerbate the existing lack of up-to-date, enforceable legislation.
Similarly, the international community is unlikely to agree on a legal or normative framework to protect organisations involved in the COVID-19 response from cybercrime or cyber espionage.
Cyber security legislation, regulation and enforcement during and after the pandemic
Cyber security legislation has failed to keep up with the rapid pace of technological developments. Although this phenomenon is global in nature, in the UK the Computer Misuse Act (CMA) is widely regarded to be deeply outdated, and no longer fit-for-purpose.[1] Even prior to COVID-19, Brexit preparations had significantly reduced legislative bandwidth in the UK, and that situation is now further compounded by the UK government’s focus on the pandemic. The likelihood of the CMA – or any other cyber security legislation – receiving attention in the foreseeable future is low.
Furthermore, enforcement of existing cyber security regulation and legislation is being reduced in order to ease the burden on organisations. Regulators across the world – notably in the EU with GDPR – are attempting to strike a balance between enabling rapid changes in data collection and processing, and protecting the rights of individuals.[2] In the UK, the Information Commissioner’s Office has also suggested they will pursue fewer investigations during the pandemic,[3] while in the US regulators have waived certain penalties and sanctions related to health information privacy.[4]
Although this pragmatism may be required, de-prioritising cyber security and data protection is likely to have negative implications in the longer term. Relaxing GDPR and other regulations to ensure healthcare provision and business continuity suggests that regulatory authorities have switched focus from the implications of a possible cyber-attack on the confidentiality, integrity and availability of systems to a confirmed threat to the availability of systems. Again, this focus on the greatest immediate threat is necessary and commendable, but attentional bias indicates that the likelihood of a successful breach whilst attention is focused elsewhere increases significantly.[5]
Moreover, there are legitimate concerns voiced by data privacy advocates that new technologies or platforms being rushed out without sufficient oversight. Most notably, there are a number of data privacy and security issues surrounding contract-tracing apps currently in development or use.[6] While in Europe EU rules such as the ePrivacy Directive and GDPR provide some oversight and minimum requirements, in the US, partisan disagreements in Congress have left tracing apps made by state authorities without sufficient data protection or security provisions.[7] More broadly, the rush towards embracing digital healthcare services during the pandemic is likely to have led to a number of new platforms and applications without sufficient security and privacy safeguards.
With regard to the enforcement of cyber-security legislation, the likely impact of COVID-19 is harder to discern. Unprecedented levels of government debt do not bode well for government expenditure on law-enforcement – particularly in a field where skills shortages result in recruitment difficulties at the best of times. On the other hand, given that only a tiny proportion of cyber criminal activity is currently investigated – let alone prosecuted – this impact may not be pronounced.[8]
COVID-19 and the protection of essential healthcare services: a new international framework?
Targeting of the healthcare and pharmaceutical sectors during the pandemic
COVID-19 has also raised questions about the long-term future of the cyber security of the healthcare and pharmaceutical sectors, given their integral role in dealing with the effects of the pandemic.
Already a popular target due to its weak cyber security maturity, the pandemic has increased the healthcare sector’s attractiveness in the eyes of cybercriminals. Although some ransomware operators openly pledged to avoid targeting healthcare organisations throughout the pandemic,[9] any examples of self-restraint have turned out to be an exception rather than a new rule of conduct. During the first half of 2020, hospitals across several geographies suffered ransomware incidents that degraded the availability of critical assets and data. One prominent incident involved University Hospital Brno, Czech Republic’s second-biggest hospital and key player in the fight against the pandemic, where an unknown ransomware strain forced the facility’s entire IT infrastructure offline and caused significant delays in care.[10]
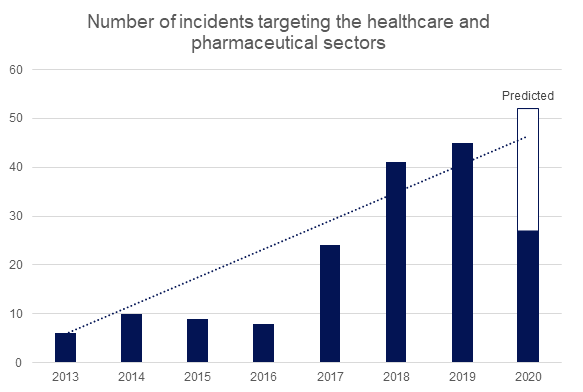 Figure 1: Orpheus’ intelligence reporting database shows the number of malicious cyber actvity targeting the healthcare and pharmaceutical sectors as of 1 July 2020.
Figure 1: Orpheus’ intelligence reporting database shows the number of malicious cyber actvity targeting the healthcare and pharmaceutical sectors as of 1 July 2020.Nation-state cyber espionage units have re-tasked their capabilities to collect intelligence on vaccine research in academic and pharmaceutical organisations. These include Iranian operations against WHO employees and pharmaceutical company Gilead; Chinese state units exploiting vulnerabilities associated with remote working tools to target the healthcare and pharmaceutical sectors; and Russia’s APT29 targeting vaccine research in the UK, US and Canada. As we outlined in our blog on vaccine nationalism, cyber espionage groups are likely to continue to focus much of their capabilities on collecting intelligence on vaccine research, given its importance.
A new legal and normative framework?
These incidents have sparked condemnation by the international community,[11] and opened up discussions about a new international legal or normative framework to protect healthcare, pharmaceutical and academic institutions involved in combating the pandemic.[12] The Netherlands, most prominently, proposed the following recommendations:
“Malicious cyber operations targeting healthcare systems or facilities could, depending on the specific circumstances, be qualified as a violation of international law. Equally, cyber enabled information operations that intervene with, for example national crisis response mechanisms during a health crisis, could, depending on the circumstances, be qualified as violation of international law.”[13]
However, given the current slow progress towards establishing international law and norms for cyberspace, we assess that the pandemic is unlikely to result in radical changes to the current framework.
Limiting ransomware operations against hospitals, for example, is unlikely to change without the expansion of the Budapest Convention, which is at present the main international instrument against cybercrime.[14] In addition to most EU countries, the US, Canada and others have ratified the convention. However, Russia, India and China have refused to ratify the convention, primarily due to what has been termed the “Balkanisation” of cyberspace.
Similarly, the pandemic is unlikely to be a sufficient catalyst for the creation of an international framework to deter nation-state activity against the healthcare and pharmaceutical sectors. The UNGEE, the UN working group responsible for creating a framework for responsible state cyber activity has made little progress since the publication of its first report in 2015, which proposed international norms to govern state cyber activity.[15] The international community’s failure to advance these proposals is again in part due to the Balkanisation phenomenon, but also stems from policymakers in the United States, who wish to retain freedom of action for their own intelligence agencies. Moreover, given that the COVID-19 pandemic is widening rather than narrowing geopolitical divisions, we do not anticipate any imminent agreements on a new international framework to protect healthcare or pharmaceutical companies.
This reiterates our previous assessment that COVID-19 is mostly reinforcing existing trends rather than creating new ones. If progress on international law to protect critical infrastructure from cyber-attacks was faltering before the pandemic, the events of the last six months are unlikely to alter this trajectory.
Deterring cybercrime and cyber espionage
There is also reason to doubt that any new international framework would deter operations against healthcare or pharmaceutical companies. Taking action against cross-border cybercriminal activity would still require significant law-enforcement co-operation between Western states and Russia and China, which is especially unlikely given the current low ebb of relations. Similarly, given that some nation-state contractors increasingly moonlight as cybercriminals, it is unlikely that domestic law enforcement will pursue criminals that also work with intelligence agencies or security services.
As for nation-state cyber espionage, while the presence of stricter international law may make threat actors more cautious, the political and economic value of successfully stealing COVID-19 research is likely to outweigh any other considerations. Moreover, the inherent limitations in making verifiable attributions of cyber espionage will allow most governments to retain plausible deniability.
Conclusion
In summary, healthcare providers and pharmaceutical companies should not expect the international community to be able to agree upon measures to protect them from malicious cyber activity. We recommend these types of organisations familiarise themselves with the tactics, techniques and procedures of ransomware and cyber espionage groups currently active.
This points to a broader problem – the lack of up-to-date legislation and the limitations of existing regulations, which are unlikely to hinder threat actors’ intent or capabilities as we look to a post-pandemic future.
[1] Orpheus is currently supporting a campaign with a variety of private sector organisations to reform the CMA: https://www.theregister.com/2019/07/29/computer_misuse_act_1990_reform_letter/
[2] https://www.darkreading.com/risk/gdpr-enforcement-loosens-amid-pandemic/d/d-id/1337920
[3] https://ico.org.uk/media/about-the-ico/policies-and-procedures/2617613/ico-regulatory-approach-during-coronavirus.pdf
[4] https://www.hhs.gov/sites/default/files/hipaa-and-covid-19-limited-hipaa-waiver-bulletin-508.pdf and https://www.hhs.gov/about/news/2020/04/02/ocr-announces-notification-of-enforcement-discretion.html
[5] https://www.sciencedirect.com/topics/neuroscience/attentional-bias
[6] https://www.bbc.co.uk/news/technology-53466471 ; https://www.amnesty.org/en/latest/news/2020/05/qatar-covid19-contact-tracing-app-security-flaw/ ; https://www.zdnet.com/article/australias-covidsafe-contact-tracing-story-is-full-of-holes-and-we-should-worry/ ; https://www.bbc.co.uk/news/technology-53485569
[7] https://www.politico.com/news/2020/07/06/coronavirus-tracking-app-hacking-348601
[8] https://www.which.co.uk/news/2018/09/exclusive-more-than-96-of-reported-fraud-cases-go-unsolved/
[9] https://www.forbes.com/sites/daveywinder/2020/03/19/coronavirus-pandemic-self-preservation-not-altruism-behind-no-more-healthcare-cyber-attacks-during-covid-19-crisis-promise/#5cef8459252b
[10] https://www.cyberscoop.com/czech-hospital-cyberattack-coronavirus/
[11] https://www.osce.org/blog/how-COVID19-will-impact-future-cyberdiplomacy and https://www.cfr.org/blog/amid-covid-related-cyber-threats-netherlands-leads-un-efforts and https://www.consilium.europa.eu/en/press/press-releases/2020/04/30/declaration-by-the-high-representative-josep-borrell-on-behalf-of-the-european-union-on-malicious-cyber-activities-exploiting-the-coronavirus-pandemic/ and https://www.state.gov/the-united-states-concerned-by-threat-of-cyber-attack-against-the-czech-republics-healthcare-sector/
[12] https://www.ejiltalk.org/oxford-statement-on-the-international-law-protections-against-cyber-operations-targeting-the-health-care-sector/
[13] https://front.un-arm.org/wp-content/uploads/2020/04/kingdom-of-the-netherlands-response-pre-draft-oewg.pdf
[14] https://www.chathamhouse.org/expert/comment/building-stronger-international-legal-framework-cybercrime
[15] https://ccdcoe.org/incyder-articles/2015-un-gge-report-major-players-recommending-norms-of-behaviour-highlighting-aspects-of-international-law/

