Part I: Origins of Balkanisation
This is the first in a series of blog posts which assess how an increasing number of nation states are seeking to disconnect their internet from the wider global internet. The decision to do so could lead to a ‘Balkanised’ internet, reflecting the breakdown of the Ottoman Empire in the 20th century into a collection of hostile and uncooperative states. It could also pose issues for organisations working in these states, as we assess throughout the series.
Introduction
Last May, Vladimir Putin signed into law a bill to explore the possible disconnection of the Russian Internet (RuNet) from the global Internet, which would allow Russian networks to continue operating in the event of a major cyberattack or geopolitical crisis.[1]
This is the latest development in the process of what has been described as the “Balkanisation” of the Internet, as an increasing number of nation-states look to reinstate their digital sovereignty by enforcing data localisation laws, new regulatory regimes, and setting up national intranets. As a result, the Internet could devolve into a series of hostile and uncooperative states and networks. This new “Splinternet” could lead to limited cross-border data flows, Internet censorship, and heightened cybercriminal activity.
The term “Balkanisation” derives from the fragmentation of the Ottoman Empire into smaller, hostile states in early 20th century. The end of the Ottoman cultural and political hegemony over the Balkans led to a near-century of military conflict and humanitarian crisis in the region. Much like the Ottoman Empire, the United States’ hegemony over the Internet is being increasingly challenged by this process, which itself is driven by a variety of actors. As a result of this process, the threat landscape is being increasingly shaped by national policies, as are businesses’ capabilities to protect themselves against these threats.
With new legislation, nation states will have unprecedented license to gain access to firms’ proprietary data. Cooperation between private and public actors will become increasingly limited by compliance and regulation. Cybercriminals heed no such state boundaries or intranets and converse freely on the dark web. The Balkanisation of the Internet further hinders cooperative efforts to fight against such threat actors, and will bring a host of challenges to businesses, tech firms and cybersecurity firms alike. As a result, cybercriminals and nation-states alike are adapting their Tactics, Techniques and Procedures (TTPs) to take advantage of this Balkanisation, meaning an increasingly unpredictable threat landscape for businesses.
In this five-part series, Orpheus will be taking a look at the variety of threats to businesses that arise from the Balkanisation of the Internet, and how businesses can mitigate these threats through a threat intelligence provider.
First, this introduction will review the events leading up to this process of Balkanisation, from the birth of the Internet to the 2013 Snowden leaks.
Second, we will take a look at challenges to businesses posed by new EU regulations such as GDPR. While it has had a positive impact overall on cybersecurity, inconsistent enforcement will hinder decision-makers and businesses. We assess that businesses will continue struggling with compliance in the foreseeable future.
Third, we will look at India and Brazil’s new data localisation laws, and their struggle with WhatsApp, whose market position in these countries is increasingly challenged by local governments, domestic competitors, and exploitation by cybercriminals. We estimate that businesses operating in these countries will be increasingly targeted by domestic cybercriminal activity, who are evolving their TTPs in response to recent legislation.
Fourth, we will consider Russia’s attempts to enforce digital sovereignty, which further threatens the security and privacy of foreign businesses operating in Russia. In addition, we estimate that Russia’s new laws, if enforced successfully, will bring significant change to its domestic cybercriminal landscape.
Fifth, we will consider China’s own digital sovereignty laws, which equally justifies malicious activities and intelligence collection on foreign firms operating within their borders. We estimate that the likelihood of sophisticated compromise techniques such as supply-chain or third-party compromise attacks will grow as a result of this legislation.
Firms are finding it increasingly difficult to comply with these countries’ regulations without giving in to state censorship or putting their data at risk. We believe that businesses operating in these states will struggle with compliance to intrusive digital sovereignty laws and will have to comply with unregulated penetration testing and minimised cross-border data flows.
Origins of the Splinternet
The origins of the Internet we know today began with ARPANET, a joint enterprise between DARPA, the US Department of Defence’s innovation research agency, and academics from various US universities. Following the gradual building of submarine cables and its first cross-Atlantic network in the UK, ARPANET evolved into a global network in the early 1990s, which saw its first wave of public and commercial users- which eventually resulted in the creation of the Internet.
From the onset, the Internet was a joint venture by American research institutions and governmental organisations, which incorporated liberal values like freedom of speech and assembly. This set the rise of US technological, cultural and political dominance over the Internet. The undisputed rise of tech giants such as Google, Amazon, Facebook and Apple (also known as the GAFA), means they now collect, process, and exchange the data of billions of users worldwide, and exert political, social and economic influence comparable to that of nation-states, further perpetuating US influence. Lack of regulation from the US government has allowed these firms to gain unprecedented access to consumer data with little respect for consumer privacy or competition law. In addition, the spread of the Internet eclipsed major powers like Russia and China, as demonstrated in this 1993 map of networks connected to the Internet (see image below). Unsurprisingly, the Internet had a low percentage of penetration in authoritarian regimes like Iran or Cuba.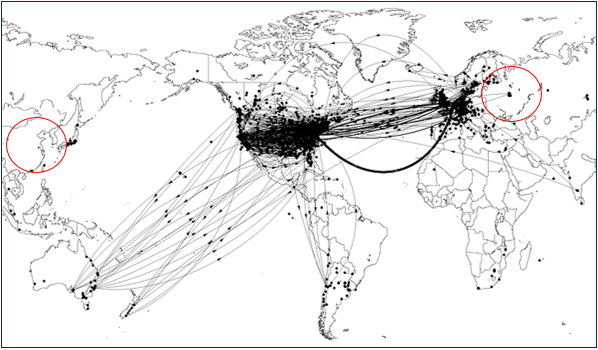
This all changed in 2013 with the revelation of the infamous Snowden leaks, which can be seen as the starting point for the process of Balkanisation. These massive data dumps of covert NSA operations and tools revealed large-scale surveillance plans by the Five Eyes intelligence agencies. Much like the current discussion surrounding Huawei, the legitimacy of these US companies was called into question because of the firms’ cooperation with state agencies, and as a result states around the world pressed for further regulation.[2]
The wave of announcements following the leaks put in motion the process of the Balkanisation of the Internet, notably with Dilma Roussef’s speech in September 2013 at the United Nations General Assembly, where she announced that Brazil would look to implement its own network and data protection laws. This fuelled a global movement to secede from the US-led Internet, as countries like Brazil, Russia, India and China (BRIC) and many others have moved to build their own sovereign networks, and with supranational organisations such as the (EU) implementing their own data localisation laws. The Splinternet was set in motion and has started putting businesses at risk in a number of countries, as cybercriminals and nation-state actors are adapting their TTPs as a result.
We will examine the impact of GDPR on businesses and cyber threat intelligence firms in next week’s post, followed by Brazil and India’s new data localisation laws the week after.
The blog series will follow the schedule below:
I: Introduction
II: GDPR and new regulatory regimes
IV: Russia’s Digital Sovereignty
III: Brazil and India’s cybercriminal boom
V: China’s Great Firewall
[1] https://www.forbes.com/sites/zakdoffman/2019/05/01/putin-signs-russian-internet-law-to-disconnect-the-country-from-the-world-wide-web/#567a2bc81bf1 Forbes
[2] https://www.theguardian.com/technology/2019/apr/24/may-to-ban-huawei-from-supplying-core-parts-of-uk-5g-network The Guardian

